高速数据链信息系统是舰艇作战信息的传输通道[1-3]。而民用船舶上同时也配备数据链系统,实现与港口指挥部门的相关数据信息交互。
因数据链系统中信息的共享性,会遭到不法分子利用非法入侵行为盗取或篡改舰船数据链传输信息,直接影响舰船数据链信息传输安全[4]。有众多学者针对舰船数据链信息加密传输方法的课题进行了研究。任仪[5]研究空间稀疏编码加密方法,通过该方法构建舰船数据链信息加密模型,按照模型中舰船数据链信息稀疏特征设计与之相对应的信息加密密钥,实现舰船数据链信息加密。但该方法的模型构建过程比较复杂,耗时长,导致数据加密的速度较慢。有学者研究数据库加密方法,利用密度峰值法实现舰船数据链信息聚类后,依据聚类结果构建舰船数据链信息数据库空间加密模型,完成舰船数据链信息加密和传输。但该方法的密钥在分发过程中容易发生泄漏情况,导致传输信道安全性下降。
针对以上方法在舰船数据链信息加密传输中存在的局限性,设计舰船数据链信息加密传输方法。通过专业密码机构设计秘钥长度为128 bit的SM4分组对称加密算法,该算法运算过程简单,安全高效,被广泛应用在数据传输的加密领域,并取得较好的应用效果。因此将SM4分组对称加密算法应用在舰船数据链信息加密传输中,并采用直觉模糊集方法对舰船数据链信息传输环境进行判断后,设计适合的传输协议,保障加密后的舰船数据链信息传输安全。
1 舰船数据链信息的加密传输方法 1.1 舰船数据链信息加密方法采用SM4分组对称加密算法对舰船数据链信息实施加密,保障舰船数据链信息安全。该算法加密解密过程如下:
1)参数设置
基本运算:SM4算法的32位字循环左移
密钥参数:加密密钥可生成轮密钥,轮密钥用
S盒:S盒输出输入都是8 bit。
设
| $ y = Sbox(x)。$ | (1) |
非线性变换
| $ Y=\lambda (X)=(Sbox({x}_{0})\text{,}Sbox({x}_{1})\text{,}Sbox({x}_{2})\text{,}Sbox({x}_{3})) 。$ | (2) |
线性变换
| $\begin{split} F =& L\left( Y \right) = Y \oplus \left( {Y < < < 2} \right) \oplus \left( {Y < < < 10} \right) \oplus\\ &\left( {Y < < < 18} \right) \oplus \left( {Y < < < 24} \right)。\end{split} $ | (3) |
合成变换
| $ T\left( {} \right) = L\left( {\lambda \left( {} \right)} \right)。$ | (4) |
2)轮函数
轮函数又称密码函数,设置轮函数输入用
| $ \begin{split} H( {{C_0},{C_1},{C_2},{C_3},rk} ) =& {C_0} \oplus T\left( {{C_1} \oplus {C_2} \oplus {C_3} \oplus rk} \right) =\\ & {C_0} \oplus L\left( {\lambda \left( {{C_1} \oplus {C_2} \oplus {C_3} \oplus rk} \right)} \right) 。\end{split} $ | (5) |
3)加密解密
SM4算法的加密解密都为32轮迭代架构,1个轮密钥仅与其中1轮相对应。将舰船数据链信息作为明文输入,设
| $ \begin{split} {C_{i + 4}} = & H\left( {{C_i},{C_{i + }}_1,{C_{i + }}_2,{C_{i + }}_3,r{k_i}} \right) ={C_i} \oplus \\ &T\left( {{C_{i + }}_1 \oplus {C_{i + }}_2 \oplus {C_{i + }}_3 \oplus r{k_i}} \right)\;\;\;\;\; i = 0,1, \cdots ,31 。\end{split} $ | (6) |
通过对加密后舰船数据链信息比特流密文实施反序处理
| $ \begin{split} \left( {{D_0},{D_1},{D_2},{D_3}} \right) =& Q\left( {{C_{32}},{C_{33}},{C_{34}},{C_{35}}} \right) =\\ &\left( {{C_{35}},{C_{34}},{C_{33}},{C_{32}}} \right) 。\end{split} $ | (7) |
该算法进行舰船数据链信息加密过程,如图1所示。
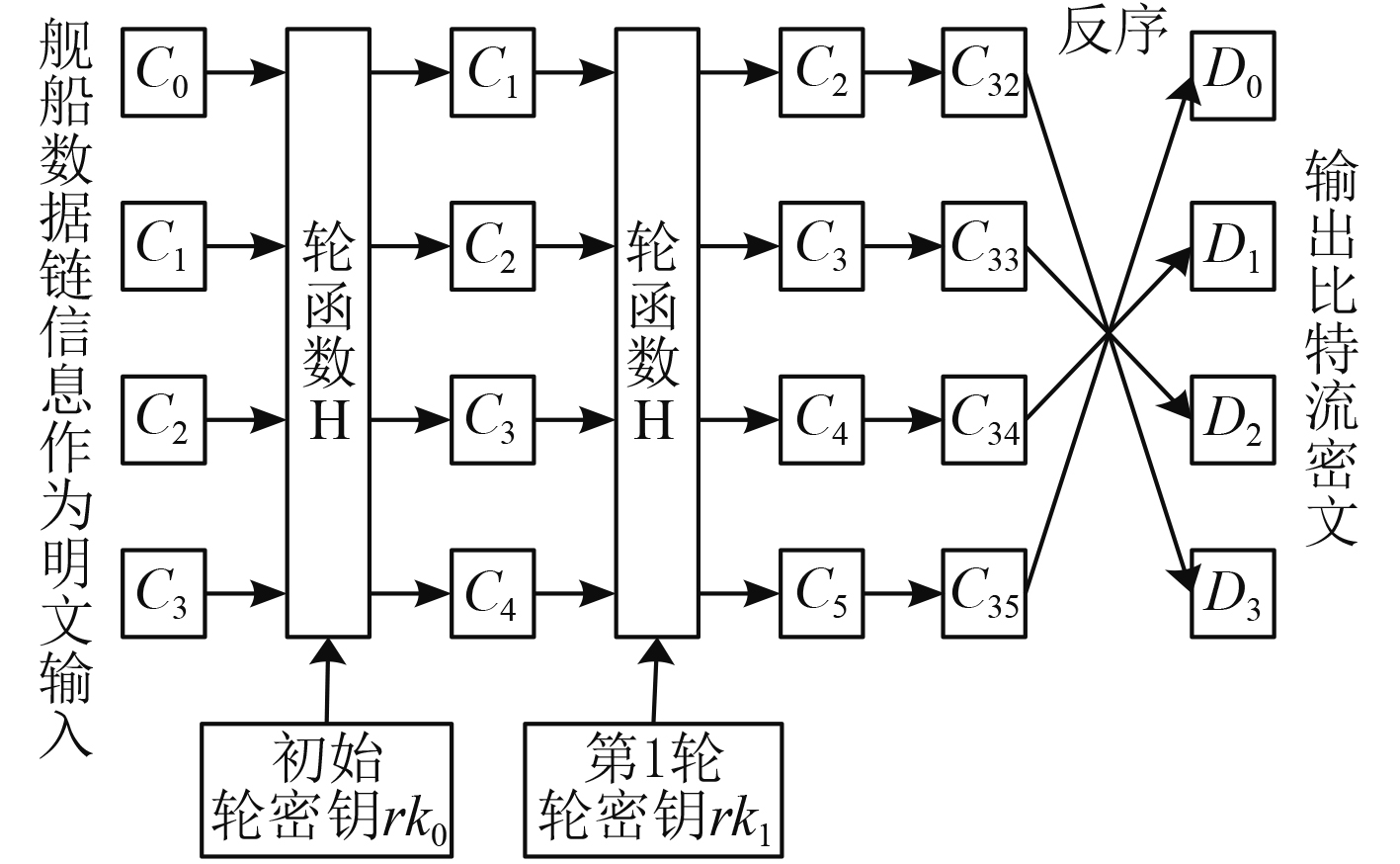
|
图 1 SM4算法的舰船数据链信息加密过程 Fig. 1 Encryption process of ship data link information based on SM4 algorithm |
可知,SM4算法的舰船数据链信息加密过程:每加密一次会处理舰船数据链信息作为明文的4个字报文,并将舰船数据链信息报文转换为比特流数据,形成1个字的新比特流密文。新密文和前3个字再次实施加密,共迭代35轮后进行反序操作,得出最后4个字比特流密文,为加密后舰船数据链信息。舰船数据链信息解密过程结构一样,但是轮密钥使用顺序相反,即解密时和加密时轮密钥使用顺序分别为
在采用SM4算法对舰船数据链信息进行加密后,对舰船数据链信息数据包实施加密封装处理,提高舰船数据链信息安全性。舰船数据链信息数据包的封装处理流程如图2所示。将舰船数据链信息传输目的端端口作为核心,以替换数据为基础,利用信息传输顶部结构得到通信地址和传输控制协议(transmission control protocol,TCP)、数据加密国际互联协议(internet protocol,IP)。在舰船数据链信息数据包加密封装中链路加密封装以密钥格式为主,通过巨量的链路节点传输信息,经数据包加密封装处理后可实现舰船数据链信息安全管理。
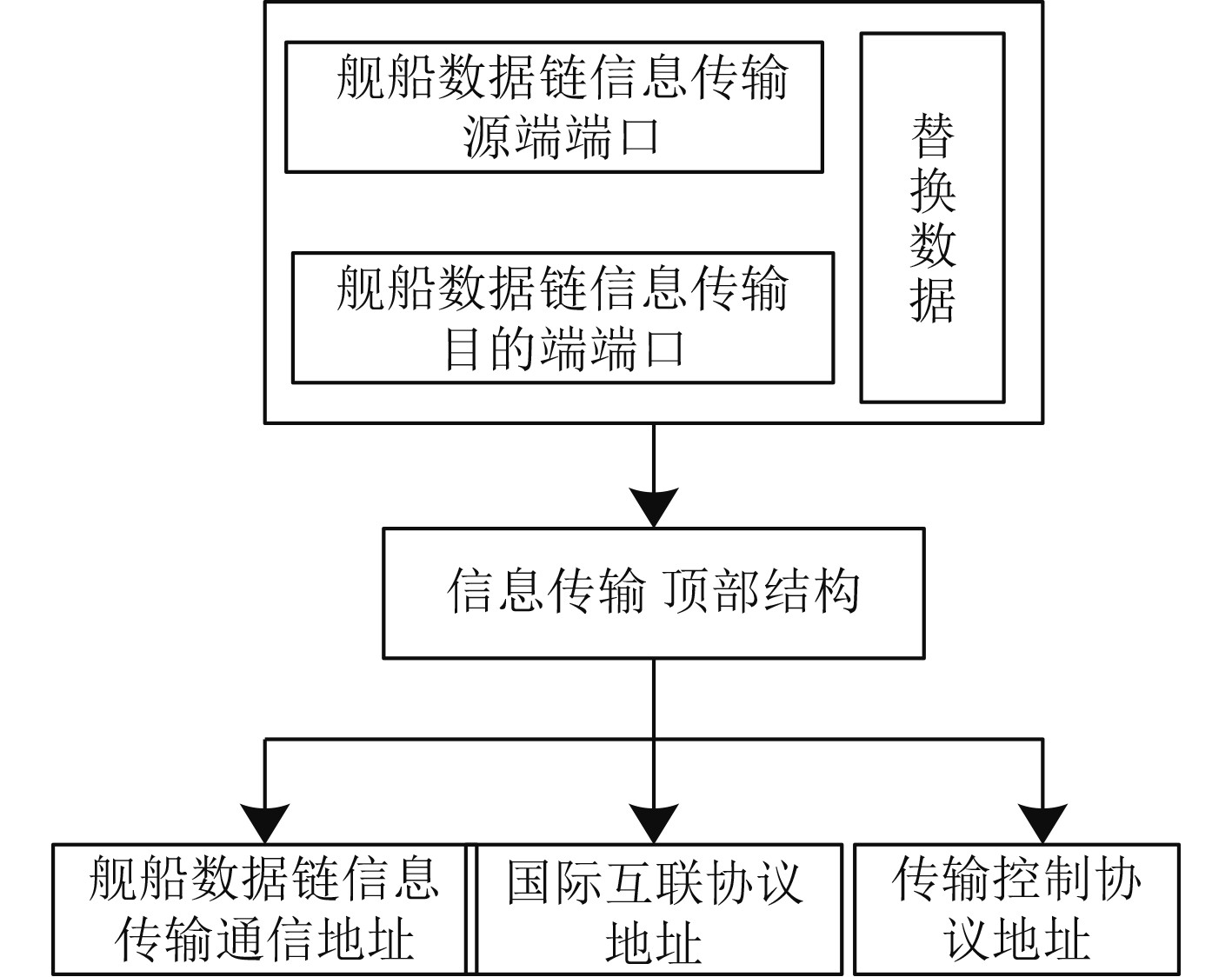
|
图 2 数据包加密封装处理流程 Fig. 2 Data packet encryption encapsulation processing flow |
经过加密、封装后的舰船数据链信息,在传输过程中,传输环境和协议的安全也直接影响舰船数据链信息传输效率,因此采用直觉模糊集方法对舰船数据链信息传输环境进行判断后,设计适合传输协议,保障加密后的舰船数据链信息传输安全。采用直觉模糊集方法对舰船数据链信息传输环境进行判断过程为:
1)利用舰船数据链信息传输属性对其传输环境实施信任判断。
2)利用专家评判法构建用
3)构建直觉模糊评价矩阵,即任意因素
| $ O \cdot W = P = \left( {{p_1},{p_2}, \cdots {p_n}} \right) 。$ | (8) |
其中:
利用评判矩阵
为了验证所研究舰船数据链信息加密传输方法,实施舰船数据链信息加密传输的有效性试验,选取某地区舰船编队中2艘舰船A,B作为测试对象。2艘舰船为具备相控阵雷达、垂直发射系统的驱逐舰,负责反舰攻击。
舰船A以2380 bit/s的速率向舰船B发送消息报文,设置舰船数据链信息队列最大容量为60000,2艘舰船之间选用Link11,Link16舰船数据链,具体数据链参数见表1。
|
|
表 1 Link11, Link16舰船数据链参数 Tab.1 Data link parameters of Link11 and Link16 ships |
选取舰船数据链Link11中6组信息,对6组信息实施置乱处理,理想情况下得出舰船数据链中6组信息位置分别为:J1=J6、J2=J3、J3=J2、J4=J5、J5=J4、J6=J1。在置乱情况下,采用本文方法对舰船数据链中6组信息进行加密传输,得出结果如图3所示。分析可知,在信息置乱情况下,采用本文方法对舰船数据链中6组信息进行加密传输后,没有发生信息丢失的情况,经过加密后信息位置与理想结果相同,说明本文方法加密传输效果较好。
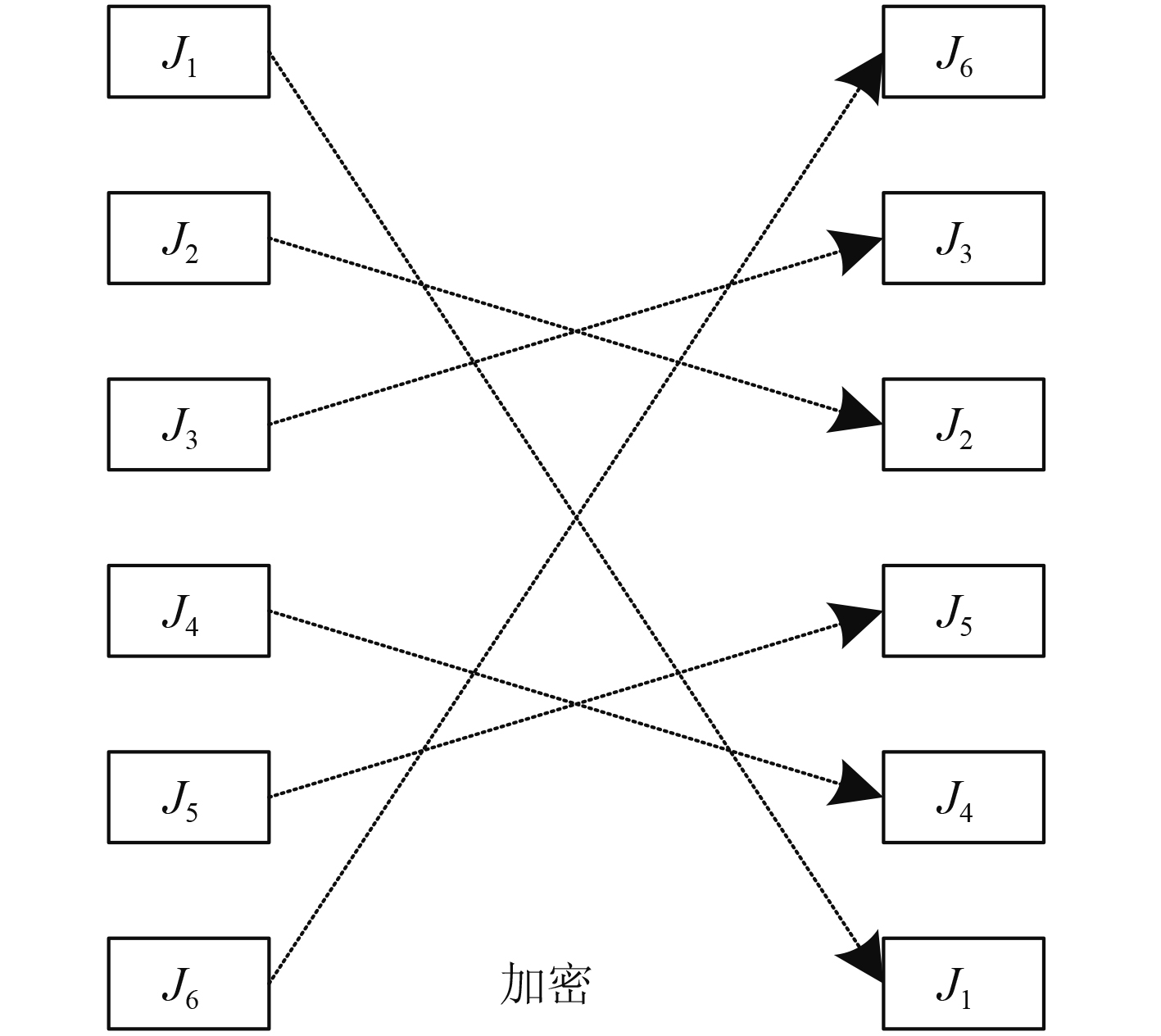
|
图 3 信息置乱情况下本文方法加密传输结果 Fig. 3 Encrypted transmission results of this method in case of information scrambling |
采用本文方法对这2艘舰船数据链信息实施加密,得出加密信息结果,如图4所示。分析可知,以发送数字123456的舰船数据链信息为例,采用本文方法对其进行加密处理。应用SM4加密方法将数字123456的舰船数据链信息作为明文,对该报文经过多次迭代后进行反序操作,得出新比特流密文。该密文只有一个与之对应专属密钥才能读取舰船数据链信息具体内容,保障2艘舰船数据链信息的安全。
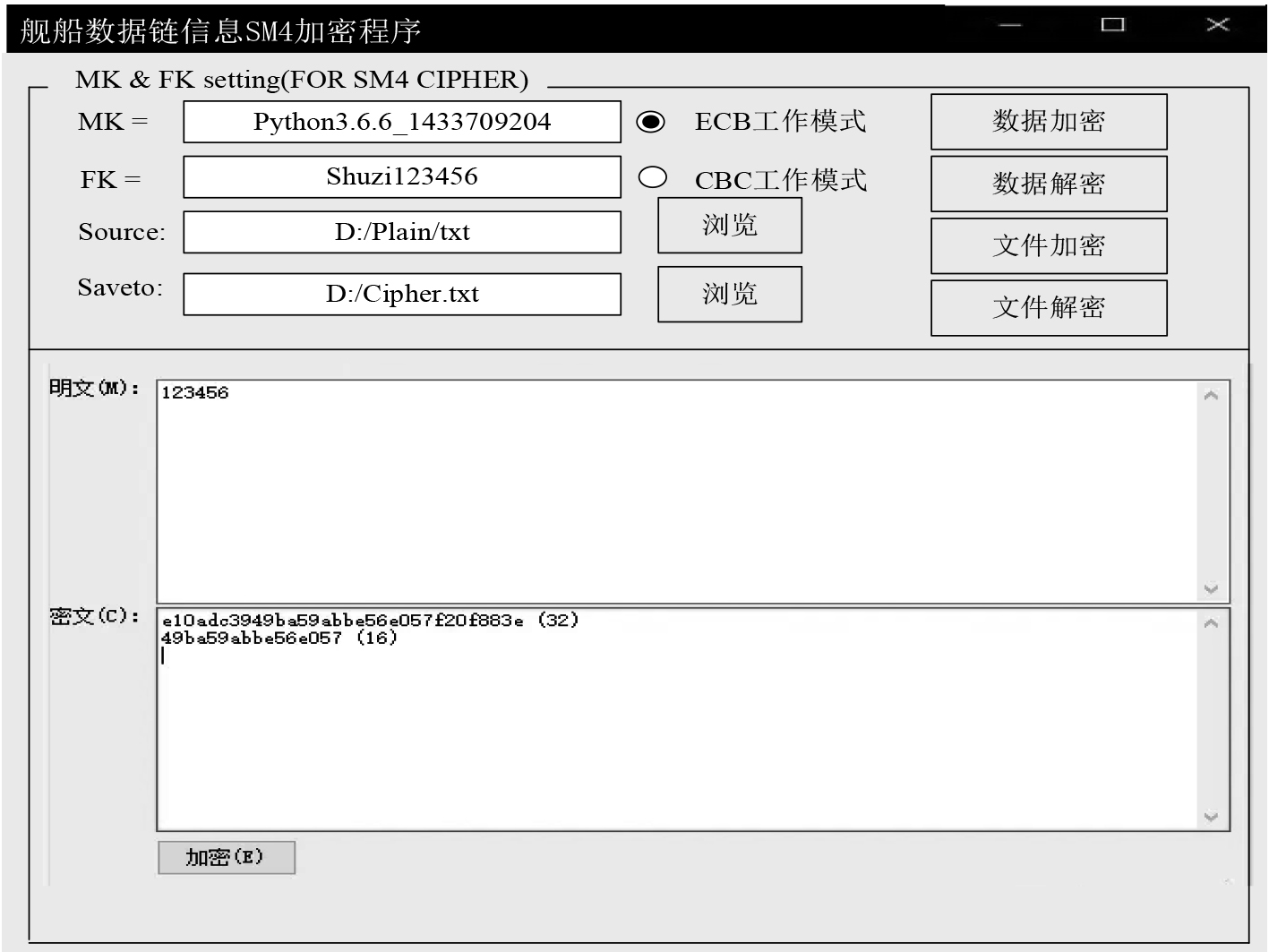
|
图 4 舰船数据链信息加密结果 Fig. 4 Encryption results of ship data link information |
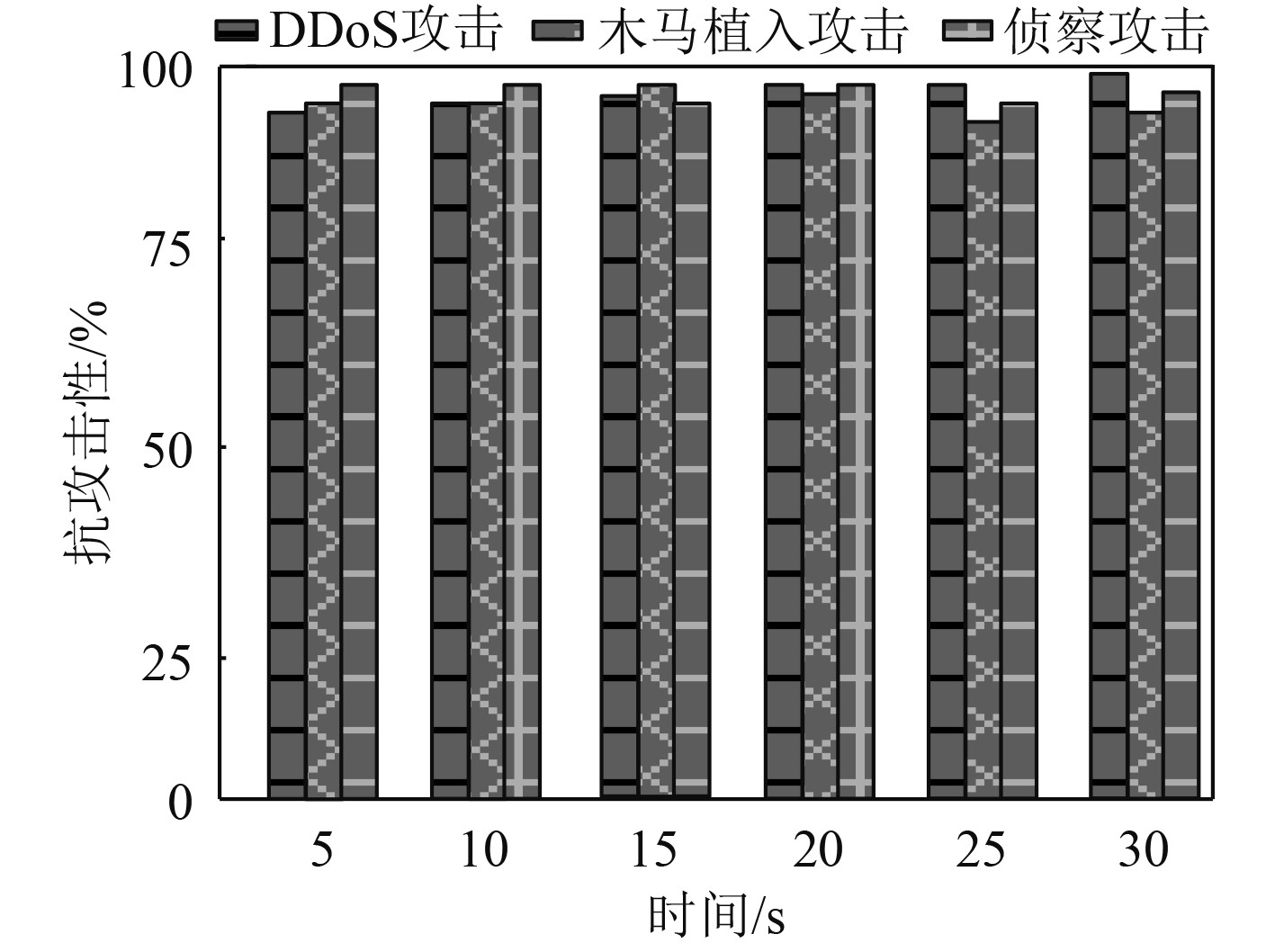
当舰船数据链Link16信息的通信网络出现非法攻击行为时,测试本文方法的抗攻击性能,测试结果如图5所示。分析可知,在舰船数据链信息通信网络出现DDos攻击、木马植入攻击、侦察攻击等非法攻击行为时,经本文方法加密后的舰船数据链信息具有较高的抗干扰性和安全性,尤其是针对DDos攻击时舰船数据链信息的平均抗干扰性高达97.5%,提高了舰船数据链信息传输效率。
|
图 5 本文方法的信息加密抗攻击性结果 Fig. 5 Anti attack results of data encryption in this method |
舰船数据链信息传输过程会受非法入侵行为影响导致信息丢失,为此研究舰船数据链信息加密传输方法,可强化信息加密机制,保障数据传输安全。通过试验验证,本文方法可以获取良好的舰船数据链信息加密传输效果。采用该方法将舰船数据链信息作为明文后,对该明文经过多次迭代后进行反序操作,得出新比特流密文。此密文仅有一个与之对应的专属密钥,才能读取舰船数据链信息具体内容,可提高舰船数据链信息安全性与抗攻击性。
| [1] |
张玉磊, 骆广萍, 张永洁, 等. 基于格式保留的敏感信息加密方案[J]. 计算机工程与科学, 2020, 42(2): 236-240. DOI:10.3969/j.issn.1007-130X.2020.02.007 |
| [2] |
杜俊逸, 肖磊, 周志恒. 基于部分空间耦合扰乱编码的数据链信息安全技术[J]. 电子科技大学学报, 2021, 50(3): 332-338. DOI:10.12178/1001-0548.2020444 |
| [3] |
张盼华, 张伟涛. 军事战术数据链信息传输技术研究[J]. 火力与指挥控制, 2020, 45(3): 167-170. DOI:10.3969/j.issn.1002-0640.2020.03.030 |
| [4] |
辜双佳, 刘万平, 黄东. 基于AES和QR的快递信息加密应用[J]. 计算机科学, 2021, 48(S2): 588-591+624. DOI:10.11896/jsjkx.210100024 |
| [5] |
任仪. 基于区块链与人工智能的网络多服务器SIP信息加密系统设计[J]. 计算机科学, 2020, 47(S1): 634-638. |
 2022, Vol. 44
2022, Vol. 44
